Expose on-premise applications with Application Gateway, and share those applications privately to Azure partners
Load balancing on-premise applications from Azure with Application Gateway is possible. The intent of this article is to explain how to achieve that, but also detail how to share these on-premise applications to a partner using Azure Application Gateway + Private Link (preview), all privately.
Load Balance on-premise applications from Azure
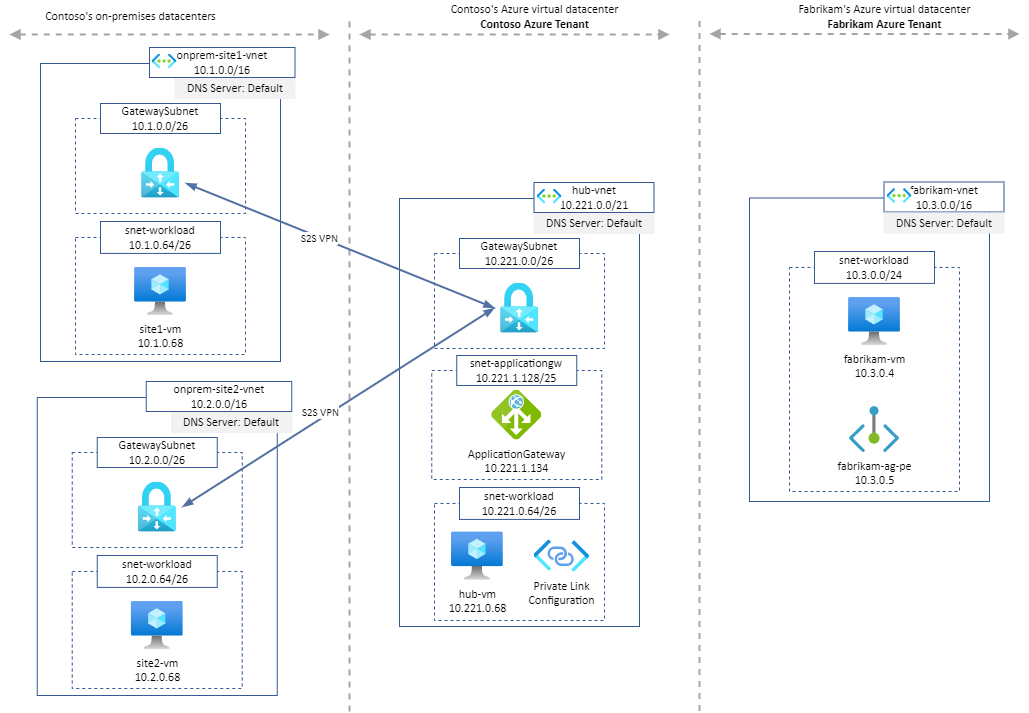
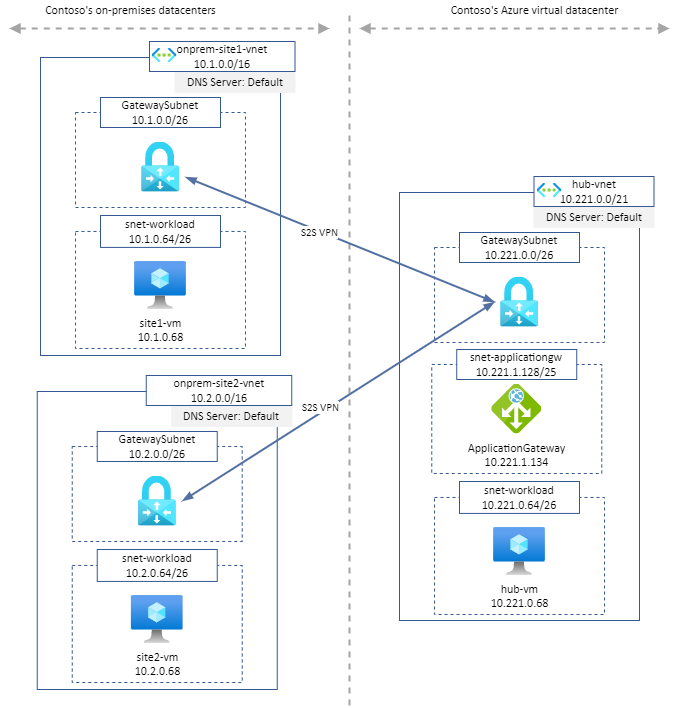
Architecture:
The terraform code to provision above infrasture is available on my GitHub.
Description:
- Two on-premises sites (emulated) are establishing S2S VPN to Azure
hub-vnet. site1-vmandsite2-vmhost an apache2 web serverApplicationGatewayinhub-vnethas a Private Listener on port80, Load Balancing HTTP traffic tosite1-vm:80andsite2-vm:80machines
This architecture is interesting when there is no on-premise load balacing solution available or if it is not possible to rely on it/them.
Load balancing illustration:
Result of $ curl http://10.221.1.134 from hub-vm:
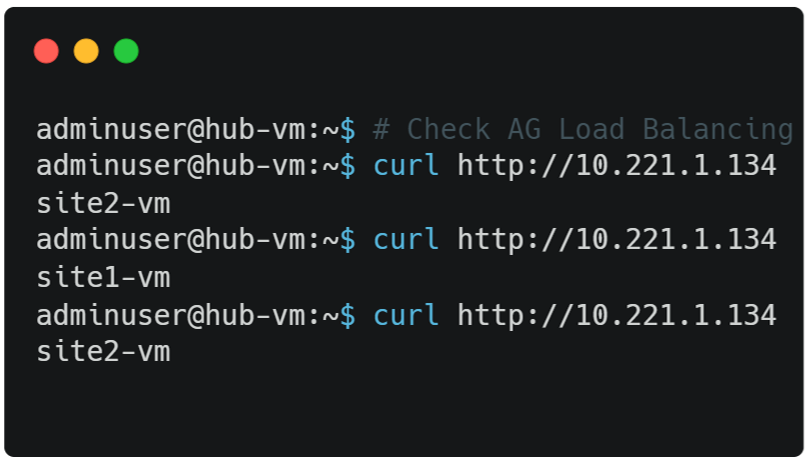
Result: Azure VMs are able to reach Azure Application Gateway which Load Balance traffic to on-premise applications.
Note: if backend machines expose websites through HTTPS using a custom (or corporate) Certificate Authority, it must be trusted by Application Gateway. It is required to upload the root certificate to Application Gateway’s HTTP Settings.
Now that we have managed to load balance traffic to on-premise applications, let’s try to share those applications with partners which use Azure.
Share those on-premise applications to Azure partners, privately!
Private link support in Azure Application Gateway is in preview since June 2022.
Let’s use this preview feature to create a Private Endpoint in Fabrikam tenant that will point to Contoso’s Application Gateway 🔥🔥.
Architecture:
Step-by-step configuration:
-
Contoso tenant: Configure Private Link configuration - it defines the infrastructure used by Application Gateway to enable connections from Private Endpoints.
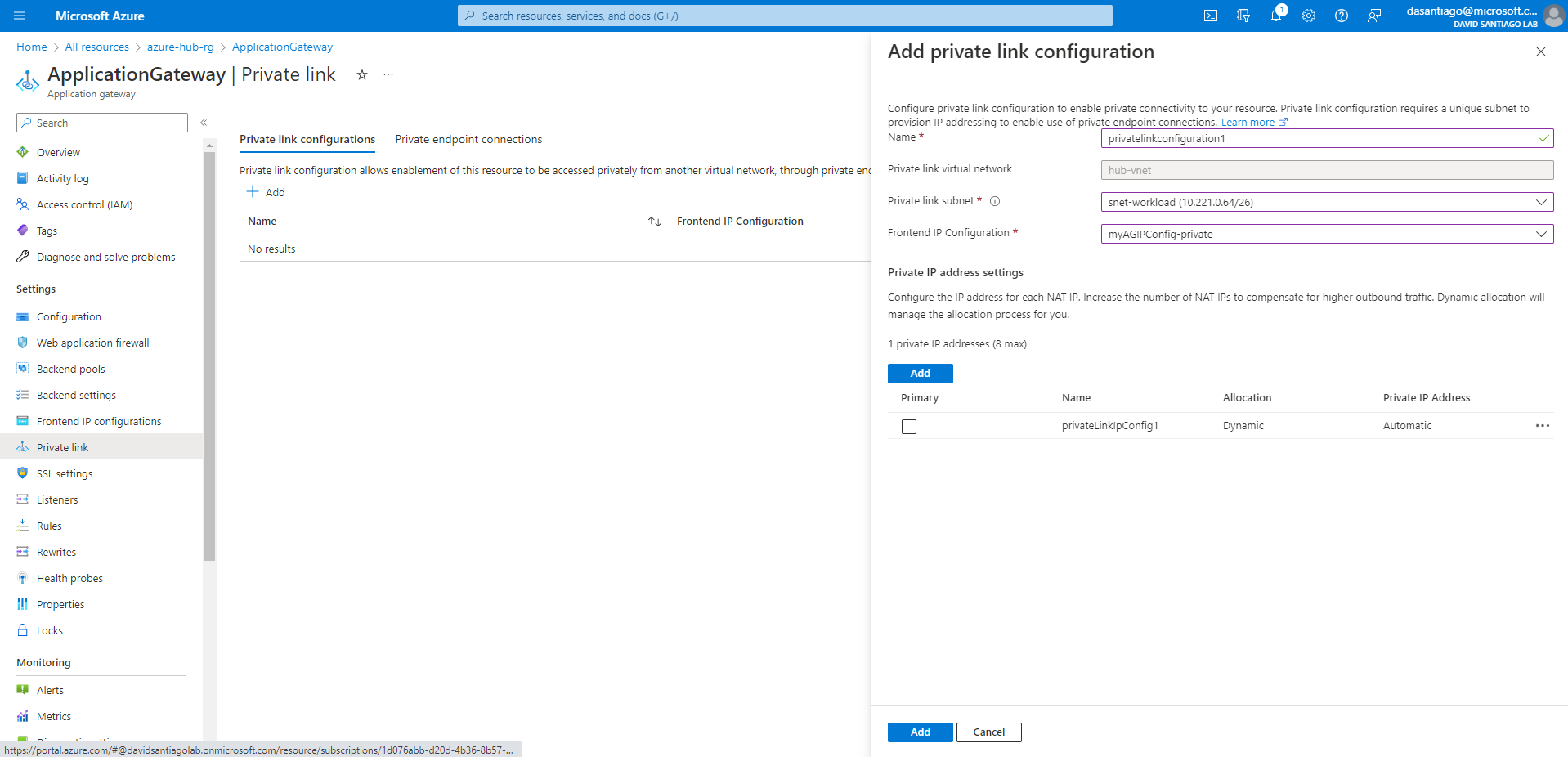
-
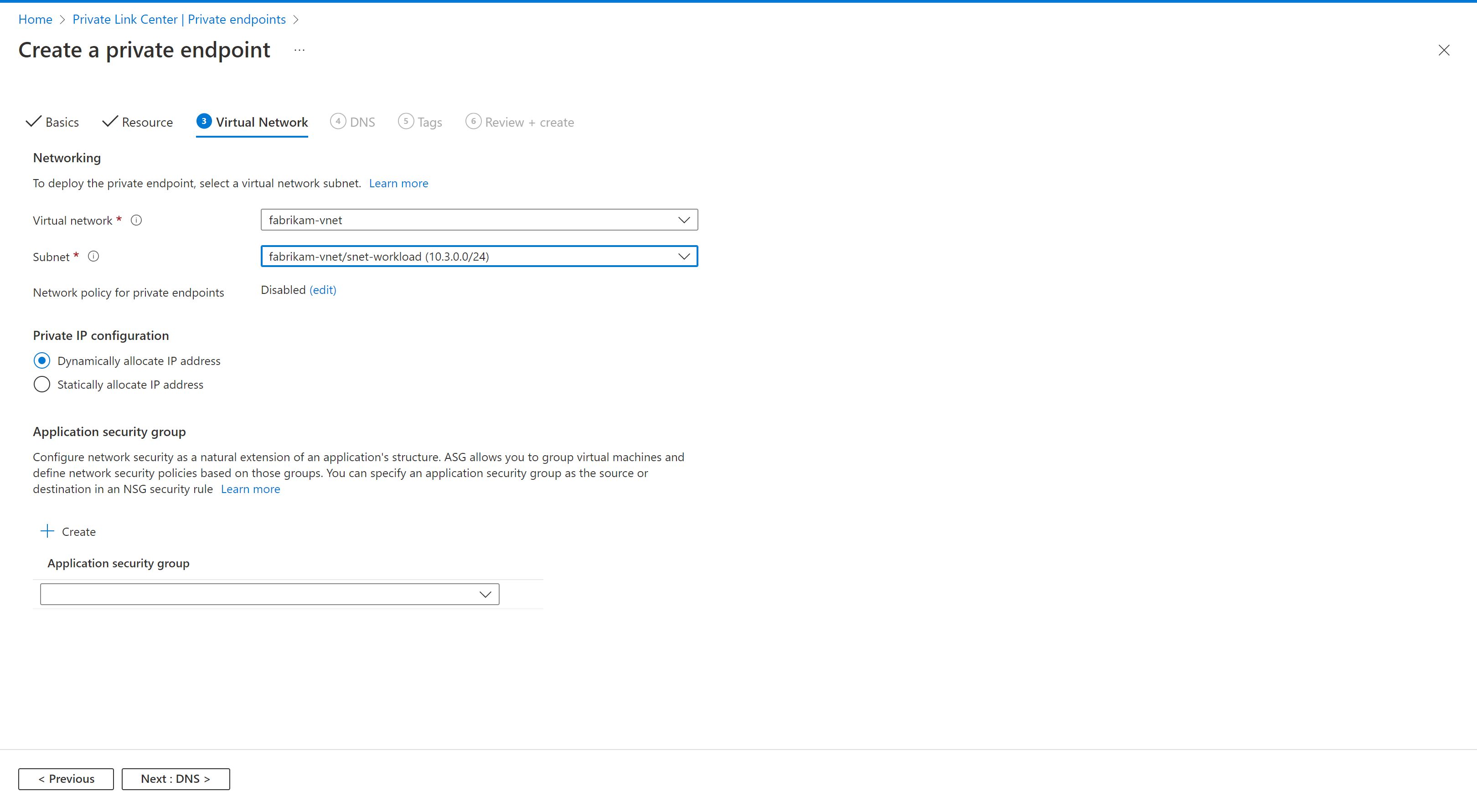
Fabrikam tenant: Create the Private Endpoint
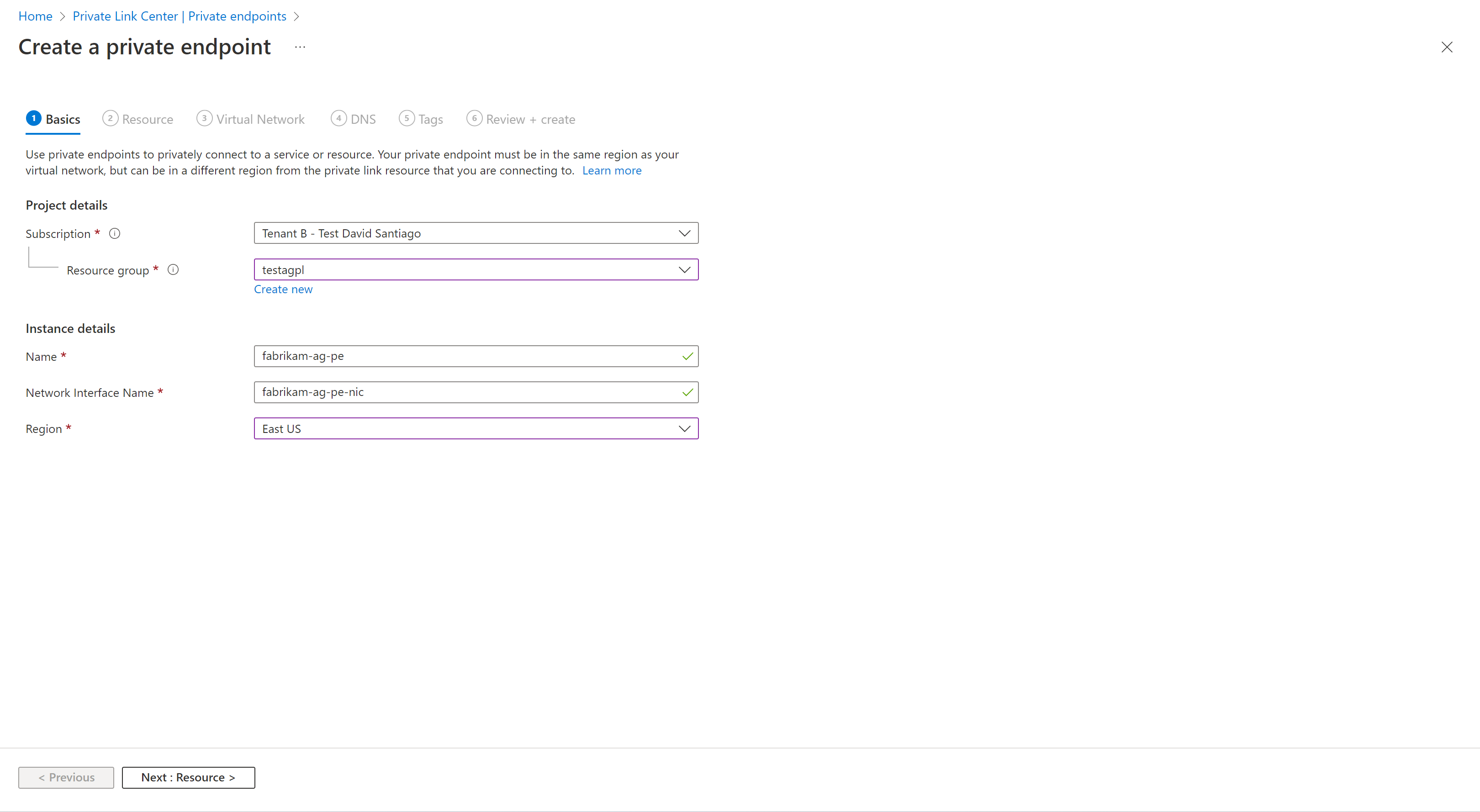
- Indicate the Resource ID of Application Gateway. Target sub-resource value must be the Private Frontend IP configuration name.
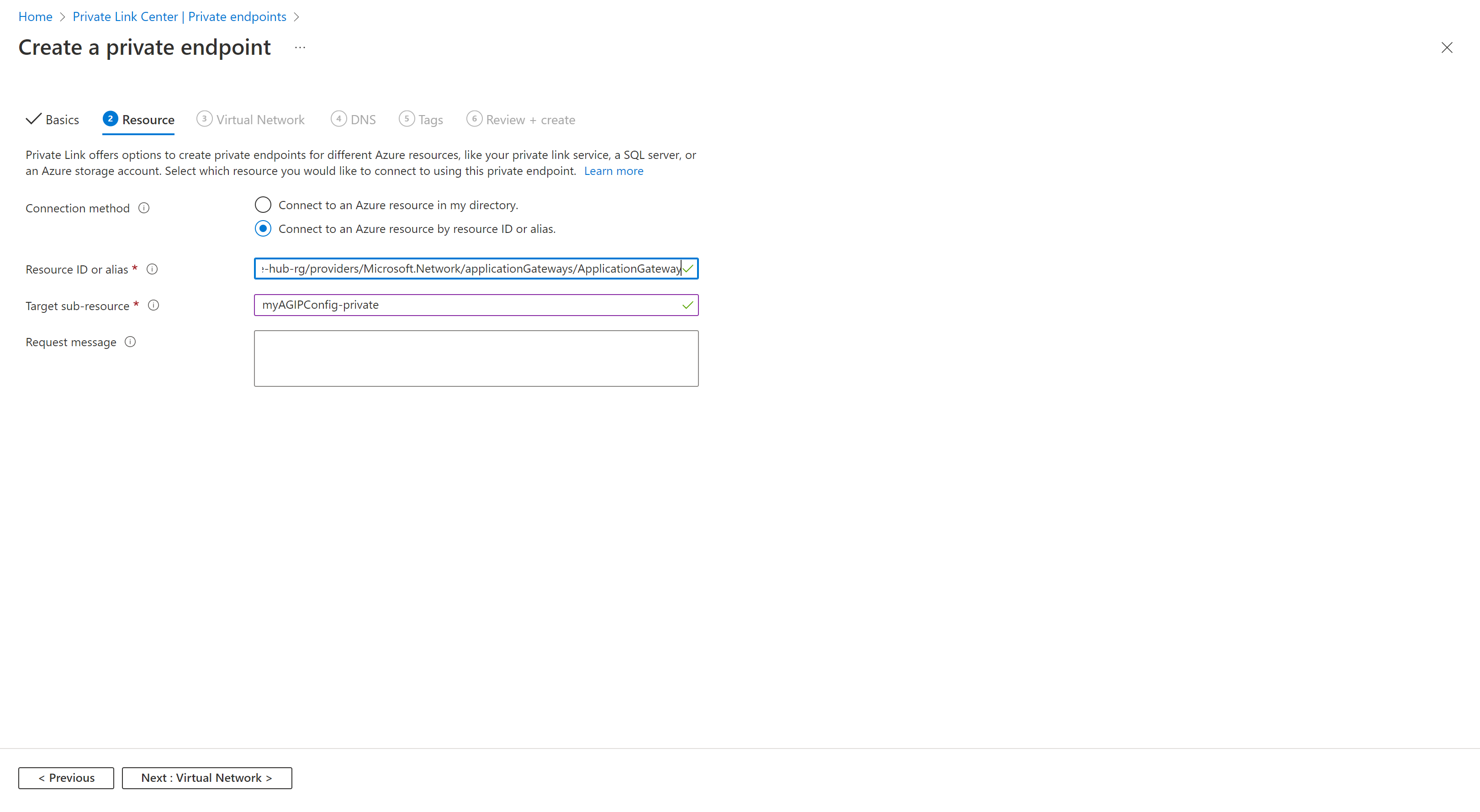
- Provide the vnet/subnet where the Private Endpoint will be created.
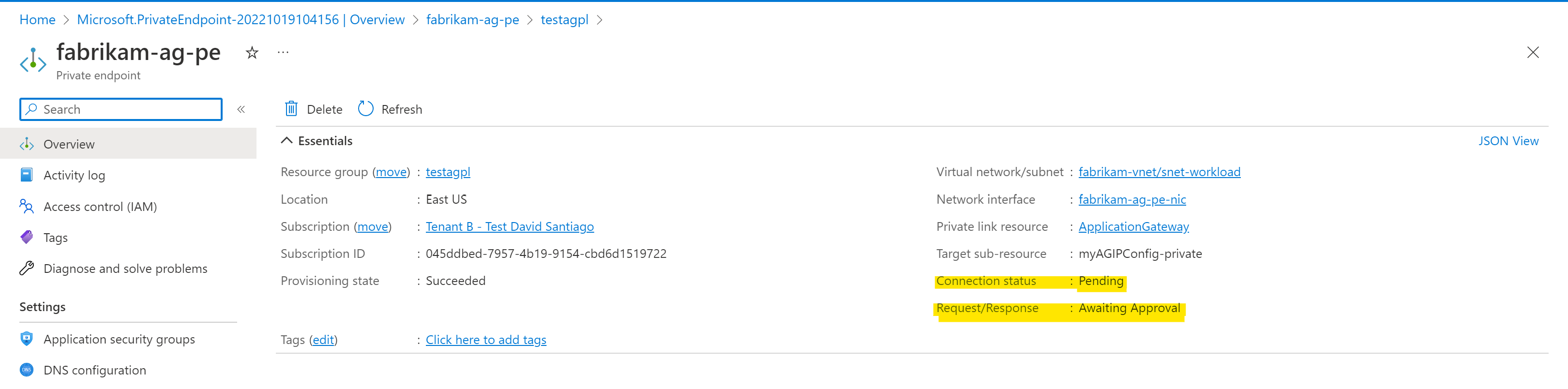
- After creation, the Private Endpoint connection status indicates Pending, it means that the connection must be approved on Contoso tenant.
-
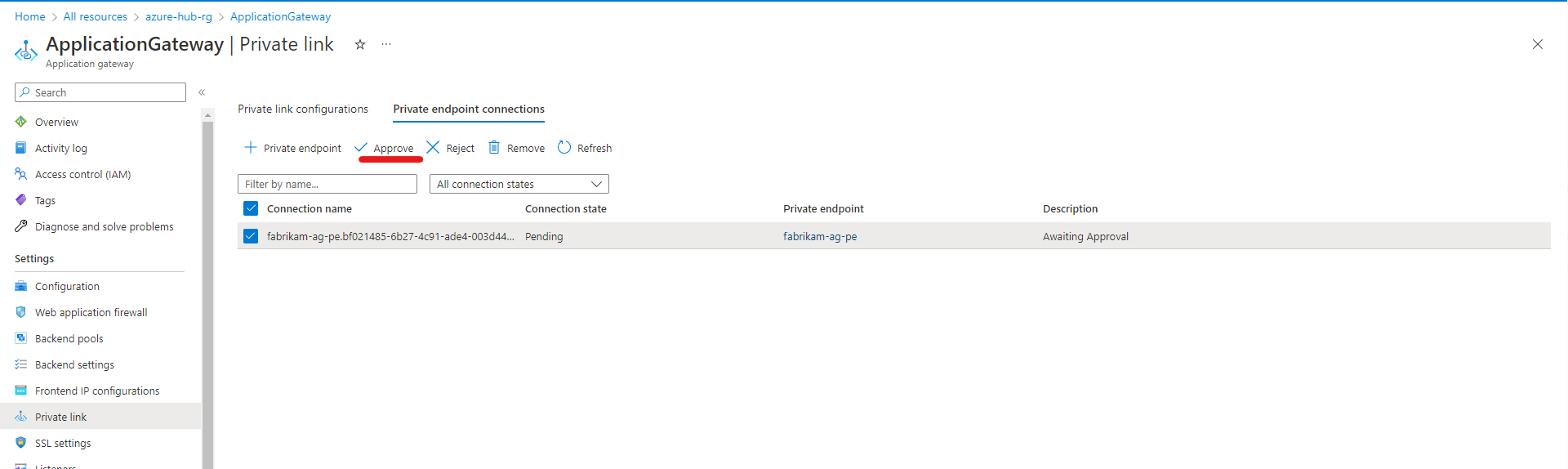
Contoso tenant: Approve Private Endpoint connection request from Fabrikam tenant
Result of $ curl http://10.3.0.5 from fabrikam-vm:
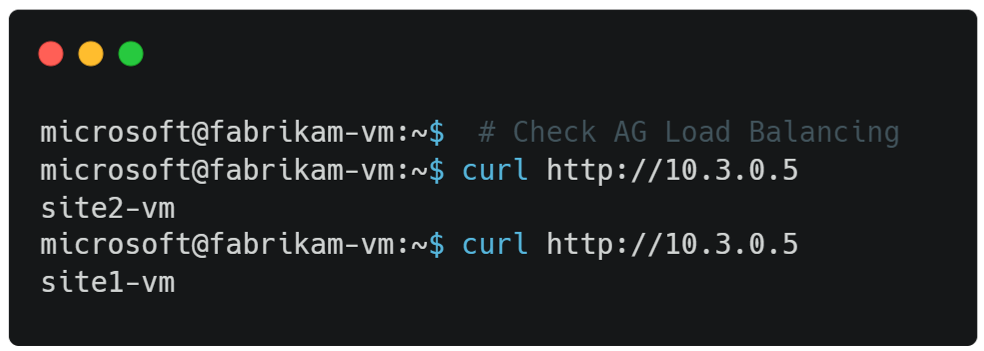
It works 🔥🔥
References
